The saarsec CTF team, comprised of both students and employees from our university, hosted their first CTF weekend workshop in June 2016. To give you an idea of what it was all about, here is a summary from one of the participants:
I heard about the saarsec team and their workshop first in our Secure Software Engineering course. Since you probably weren’t there, here’s what they’re doing: The team takes part in so-called Capture the Flag competitions. The principle behind those contests is the retrieval of flags, in this case simple strings, which are hidden in services that have to be hacked. There’s a wide range of possible services from things like web forums, which are vulnerable to some kind of attack, to compiled programs which have to be disassembled to get to the flag. Every retrieved flag gets the team some points, the winner team is selected when the competition ends at a predefined time.
In Attack-Defense style CTFs the team has to defend their own server with services running on it while attacking the machines of all other teams. As you might imagine, this is where the real magic happens. Hacking hostile servers while defending your own services as a team is so much fun that you could get addicted.
But how do I even get the skills to hack all those things? Here’s where the workshop really comes in handy. From the first minute onwards I noticed that the workshop was designed to please students interested in informatics with every skill set, from beginner to pro. The goal was to ensure that everyone was capable of playing in a full-scale Attack-Defense CTF on Sunday afternoon.
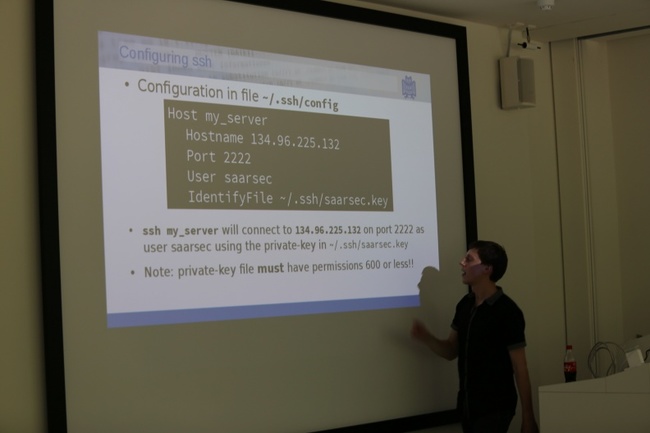
The workshop started on Friday afternoon with an introduction, followed by all the basics you need to know about how to work with a Linux-based server. Each workshop topic was separated in a presentation and an exercise section so you really learned the stuff the speakers were talking about.
During each exercise on the different topics there were multiple experienced saarsec members around to help out and answer questions. On the other hand, there were some really challenging task waiting for the faster students so it didn’t get boring, even for those which were already familiar with the topics.
On Friday evening we had dinner at Ratskeller where team members were happy to answer any questions about CTF contests, their huge success at ruCTF (read more) or everything else you might ask.
The next day started at 10 am with a security primer and an introduction of useful browser tools. A saarsec member showed us how to find vulnerabilities and exploit them only with our browser and some useful extensions. The fun thing about that, as about every other topic handled in the workshop, was, that all the attacks we talked about were “real”, not just something working only on some preconfigured workshop sites. That’s why Ben Stock, a security researcher at the CISPA, taught us already on day one the German law regarding all the things we were going to talk about and reminded us on that during the workshop.
The best thing about the exercises we did after each talk was that there was a scoreboard which rated all of us based on the numbers of hacked challenges. This feature made us all to compete against each other, take the challenges seriously and learn even more. It was clear that some of us were already experienced in some of the topics and therefore were faster than others but it was really amazing to see all of us being 100% concentrated and learning that much in so little time.

The Saturday continued with talks and exercises about SQL Injection for attacking improperly configured sites and their databases, Python for automating the attacks on the vulnerabilities we found and finally File Inclusion and Command Injection for making the website do what we want. We also had a tasty lunch break of course.
On Sunday we had a follow-up part about Python before it got really awesome. After having a small How-To lecture on Attack-Defense based CTFs, we ordered pizza and were separated in teams. To guarantee a fair CTF, the scoreboard leaders were assigned to be team captains. The remaining participants were then assigned accordingly to the teams.
Each team got access to a server as well as some information about how to submit flags they found. We learned some Do’s and Don’ts in the How-To talk but nothing could prepare us for the excitement we felt when we finally started to defend our machines and to attack the other workshop participants.

Each team had a live scoreboard where we could see how we perform. It was an intense race of finding vulnerabilities, attacking other teams and defending and fixing our services at the same time. Each team separated themselves in smaller teams working on different services simultaneously.
We had a lot of fun and even in the four hours of the contest you could feel that you learned something new in every minute you participated in the workshop. Having the opportunity to spend a great weekend, to learn a lot about real world vulnerabilities and attacks and to be able to enter the saarsec team and compete with them in the following CTFs was one of the highlights of my ongoing studies at Saarland University and I can highly recommend to register for the next workshop.
Which, by the way, takes place from 21.10 to 23.10: Go here: Workshop info

